
Network transformation
Explore the latest in cyber security with CyberOne insights. Stay ahead with expert advice, Microsoft Security updates and real-world case studies to strengthen your cyber resilience.
- All Blog Posts
- Cyber Security
- Microsoft
- Cyber Attacks
- General
- Penetration Testing
- Best Practice
- Managed Detection & Response (MDR)
- Threat Intelligence
- Choosing a Provider
- Cyber Threats
- Case Study
- Cyber Hygiene
- IT Managed Services
- Security Operations Centre
- Data Security
- Certification
- Cloud Security
- Incident Response
- Network Transformation
- Artificial Intelligence
- Budgets
- Governance, Risk & Compliance
- Identity Management
- Extended Detection & Response (XDR)
- Zero Trust
- Internet Security
- Partner
- Stories From The SOC
- Supply Chain Risk
Partner
March 23, 2026
From Partnership to Pipeline: How CyberOne & Microsoft Are Creating Security Growth for Partners
At "From Partnership to Pipeline: The Microsoft Security Growth Opportunity", CyberOne’s first partner event of 2026, one message came through clearly. The Microsoft Security...


Zscaler Private Access (ZPA) is a cloud-native security platform designed to provide comprehensive…

18 June 2019
Calculating the Cost of Network Downtime - What’s the Cost?
A primary function of most businesses is to maximise revenue while keeping associated costs under…

09 April 2019
Zscaler Introduction to Secure Cloud Transformation
We all remember when cyber security was simple, when firewalls and Anti-Virus provided effective…

08 August 2018
Zscaler Deployment Guide – Insider Tips for Deploying Zscaler
Built 100% in the cloud, Zscaler delivers your 'Security Stack-as-a-Service' from the cloud - where…
18 March 2015
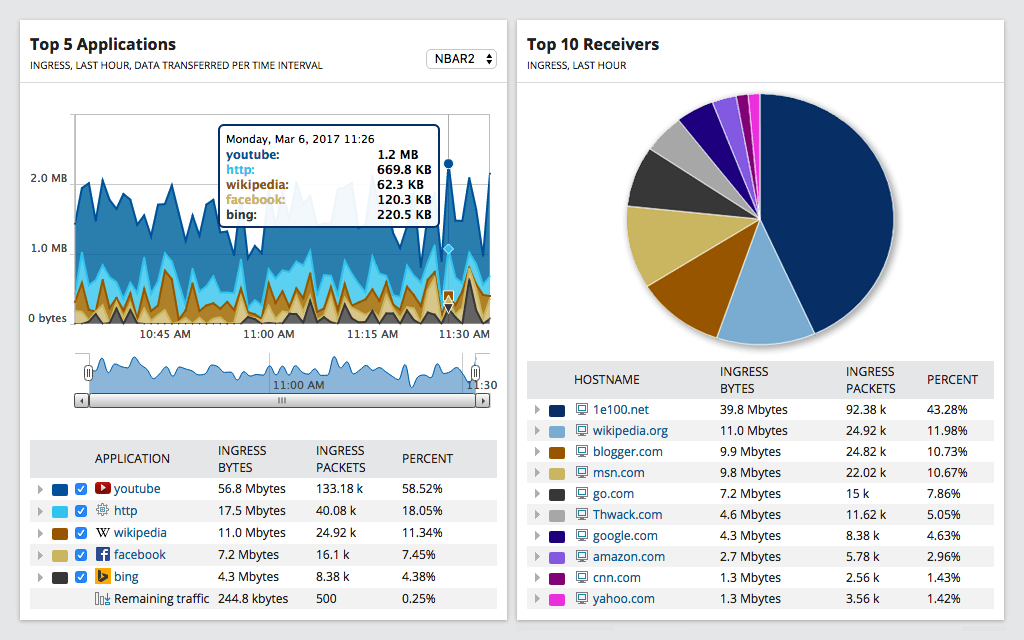
Using SolarWinds' Network Traffic Analyser to Monitor File Sharing
IT Directors strive to understand the effect of “consumerisation of the enterprise” on their…

